Top Crypto Exchange Security Audit Providers: 8 Best Blockchain Auditors Reviewed
Running a crypto exchange in 2026 is like steering a cargo ship through pirate-infested waters. In 2025 alone, on-chain attackers stole more than $4 billion from protocols and exchanges, according to Datawallet. Each new breach drives traders toward platforms they perceive as safer, while regulators under Europe’s MiCA and a growing patchwork of U.S. state rules now insist on an independent security audit before issuing a license. This guide compares eight leading audit firms so you can choose the partner that best protects your keys, credibility, and bottom line.
Crypto exchange security landscape in 2025–2026
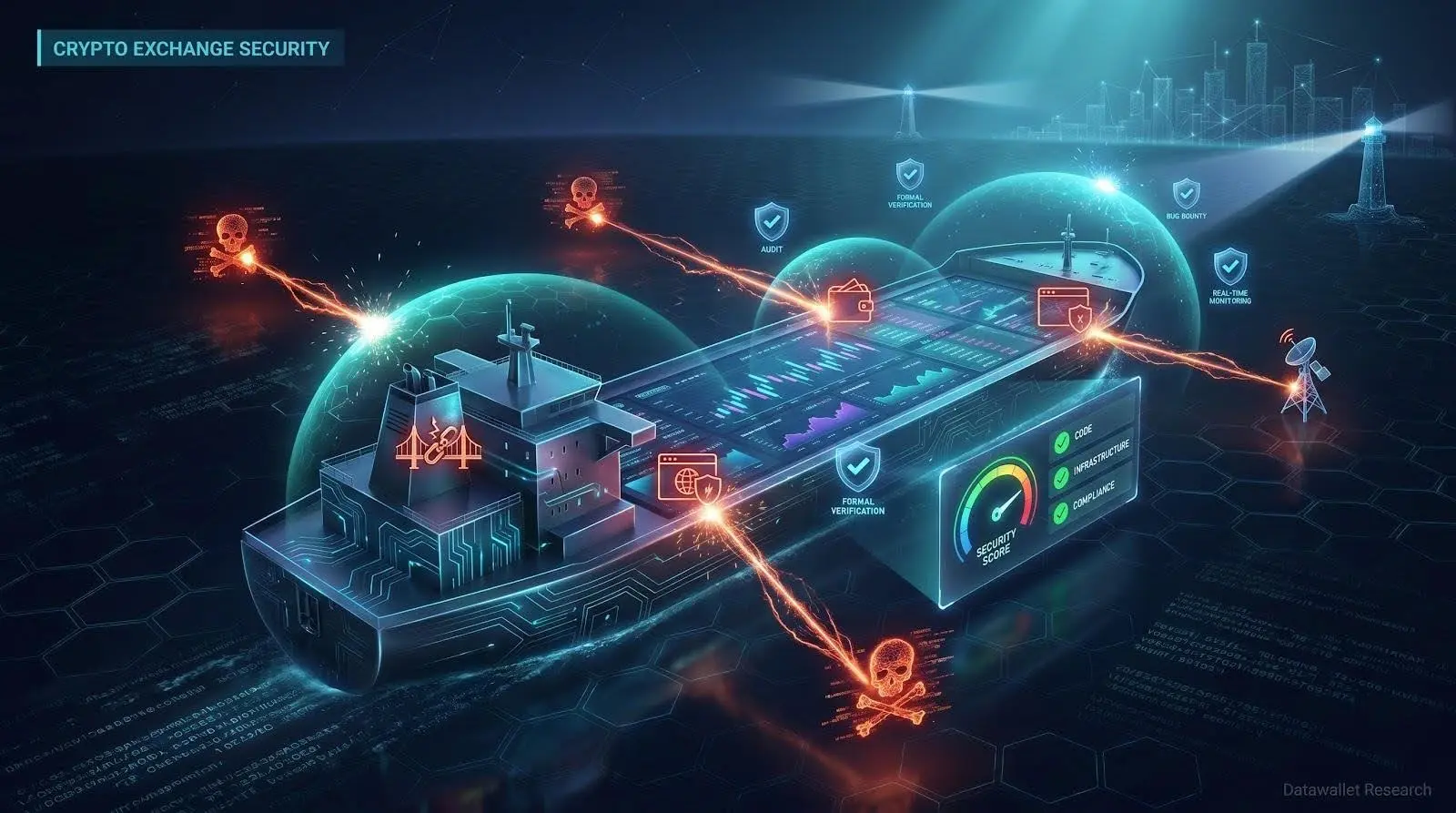
Wave of high-profile breaches
Analysts recorded more than $4 billion in on-chain losses during 2025 alone, eclipsing 2024’s total.
These were not abstract “DeFi-only” exploits; several centralized exchanges lost hot-wallet funds after the smart-contract bridges they relied on were drained. Attackers now chain vulnerabilities across web front ends, custody code, and oracle feeds in a single strike.
For teams like ours, the takeaway is blunt: even well-funded platforms with bug-bounty programs and name-brand audits still post public post-mortems. The threat surface keeps widening as exchanges add staking, cross-chain swaps, and layer-2 integrations. Each new module is another door an attacker can test.
In this climate, choosing the right auditor is not a compliance checkbox. It is the visibility that lets us close those doors before someone forces them open.
(Next up: how new regulations turn that visibility into a hard requirement.)
Regulatory heat is rising
Lawmakers have moved from polite curiosity to pointed demands. Europe’s MiCA rulebook now requires any crypto platform that touches customer funds to commission independent security and risk assessments before launch.
Across the Atlantic, state-level licensing teams ask for an auditor’s letter the same way banks ask for proof of funds. New York’s latest BitLicense guidance goes further, insisting on evidence of ongoing monitoring, not a one-time PDF. Insurers follow that lead, pricing coverage based on who last reviewed your code and how many critical issues they flagged.
No credible regulator will accept “trust us” anymore. If we want to serve customers in multiple regions, we need an audit trail as clean as our ledger, signed, version-controlled, and ready for scrutiny at renewal time. That pressure has doubled waitlists at top audit firms and pushed newer providers to specialise in rapid, regulator-friendly reviews.
(Up next: why some audits fail and how to spot the rubber stamps before they cost you.)
Community skepticism and audit challenges
Seasoned developers remind us that an audit report is only as good as the people behind it. Stories circulate of firms breezing through checklists, stamping “passed,” and moving on. A viral Hacker News thread captured the mood: “Audits are such a joke if all they do is grep for require statements.” That skepticism forces us to inspect methodology before we sign an engagement letter.
Several projects that flaunted shiny audit badges were hacked weeks later. In one example, a PeckShield-reviewed protocol lost $130 million when a price oracle went haywire. Episodes like that teach us to study process, not the logo on the cover. Does the firm fuzz test? Do they model economic exploits? Will they verify fixes before closing the ticket?
Costs add to the challenge. Elite research houses quote well into six figures for complex exchange stacks and can be booked for months. Teams racing a token-generation event sometimes choose the quickest slot, even if depth suffers. That shortcut may secure a launch date while mortgaging long-term credibility once customers notice the gaps.
Emerging trends we need to track
Auditors are adapting. Continuous-monitoring dashboards now watch contracts around the clock and alert teams and insurers when risk scores change. Formal verification, once an academic exercise, is moving into production pipelines, catching edge-case logic before humans see it.
AI is also joining the toolkit. Vitalik Buterin calls AI-assisted formal verification “one application I’m excited about” because hidden bugs remain Ethereum’s largest technical risk. He expects the tools to shorten review cycles without lowering the bar. Credible auditors still warn that machine learning is a co-pilot, not an autopilot; experienced engineers must interpret the findings.
According to Project 11’s March 2026 “Lattice HD Wallets” release, the company open-sourced a Rust implementation of hierarchical wallets that use lattice-based signatures, giving auditors a concrete codebase and threat model to test whether an exchange’s key-management flow will stay intact once quantum computers mature. For exchange leaders mapping the transition, Project 11’s primer Quantum Blockchain 101 explains why Shor’s algorithm makes today’s elliptic-curve keys fragile and spells out the NIST deadlines that require wallets and protocols to migrate well before 2035.
Taken together, the message is clear: the market no longer tolerates surface-level audits, yet demand for deep reviews has never been higher. Knowing which firms truly innovate and which ones sell stickers disguised as security is now part of our core risk-management playbook.
(Next, we will walk through the criteria we used to separate leaders from passengers and share a table that maps each auditor against those filters.)
How we chose the top audit providers
We reviewed dozens of security firms and kept only eight. Our goal was clear: highlight auditors whose work genuinely reduces exploit risk for exchanges, not those with flashy marketing pages.
First, we checked track records. An auditor that has examined hundreds of contracts yet shows a near-zero post-audit exploit rate ranks higher than one with colorful dashboards but clients chasing refunds. Public reports, GitHub disclosures, and community feedback guided this filter.
Next came technical depth. We wanted teams that can move from Solidity to Rust to Kubernetes within the same engagement. Formal verification, custom fuzzers, and hands-on penetration tests signaled real skill; automated scanners alone did not.
Exchange-specific experience mattered. Wallet management, API abuse, and proof-of-reserve math are pain points a DeFi-only auditor may never see. Providers that have hardened hot-wallet rotations or stress-tested matching engines earned bonus credit.
Transparency followed. The best firms publish detailed findings and confirm fixes before signing off. Those that hide reports behind permanent NDAs or deliver one-page “all good” summaries did not make the cut.
Finally, we balanced cost, speed, and post-audit support. Enterprise teams can wait four months if the review is surgical; startups often need a faster, leaner option. We rated each auditor on typical turnaround time, engagement minimums, and whether they provide continuous monitoring after the paperwork is signed.
The next table distills these criteria so you can compare strengths and gaps at a glance.
Quick-scan comparison table
Use this matrix to align each auditor’s strengths with your timeline, budget, and risk profile.
|
Auditor |
Founded |
Core strength |
Notable exchange clients |
Typical turnaround* |
Cost band† |
Formal verification |
Continuous monitoring |
|
CertiK |
2017 |
High-volume formal proofs |
Binance, OKX |
3–5 weeks |
$$ |
Yes |
Skynet |
|
Trail of Bits |
2012 |
Deep research and zero-day hunting |
Coinbase, dYdX |
6–10 weeks |
$$$ |
Yes |
Optional |
|
Hacken |
2017 |
Pen testing and proof-of-reserves |
Gate.io, KuCoin |
4–6 weeks |
$$ |
Limited |
HackenProof alerts |
|
Halborn |
2019 |
Offensive security across full stack |
Crypto.com, Binance US |
5–7 weeks |
$$ |
Partial |
SOC2 dashboards |
|
SlowMist |
2018 |
Asia-focused threat intel |
Huobi, OKX |
4–6 weeks |
$$ |
No |
MistTrack |
|
ConsenSys Diligence |
2017 |
EVM expertise and fuzzing |
Uniswap, Aave, Coinbase |
5–8 weeks |
$$ |
Yes |
Fuzzing League |
|
OpenZeppelin |
2015 |
Standard-library auditors |
Coinbase, MakerDAO |
4–7 weeks |
$$ |
Yes |
Defender |
|
Quantstamp |
2017 |
Scalable multi-chain coverage |
Binance, Flow |
3–5 weeks |
$$ |
Limited |
Security Network |
*Based on a mid-size exchange audit in 2026.
†Relative scale: $ – lower, $$$$$ – highest.
Formal-verification and research giants
CertiK: scale meets math-level assurance
CertiK started in a Yale lab and now audits code that protects roughly half a trillion dollars in market value. The team relies on formal verification—mathematical proofs that a smart contract cannot break its own rules—to catch edge-case logic long before real money is at risk. Public stats tell the story: more than 5,000 audits across 20 chains and over 600 billion USD protected.
For exchanges juggling hot wallets, staking modules, and bridge contracts, that depth matters. CertiK engineers build custom models to simulate issues from re-entrancy loops to rounding errors in withdrawal math. When the code passes, they plug it into Skynet, a live dashboard that scores risk every time a contract interacts on-chain. Insurers increasingly treat a high Skynet score like a credit rating, trimming premiums for desks that maintain it.
Speed is another draw. With more than 250 security specialists on staff, CertiK can field multiple squads at once, so most exchange-grade audits finish in about a month, a quick turnaround for work this deep. Pricing sits in the upper quartile, yet founders report that major investors recognise the brand and rarely question the spend. If you want the most widely recognised “seal of mathematical approval,” CertiK is still the obvious first call.
Trail of Bits: elite security research and engineering
Trail of Bits approaches audits like cold-case detectives; no assumption survives contact with their engineers. The New York team has dissected everything from Ethereum’s Constantinople upgrade to Algorand’s consensus code, often finding chain-stopping flaws days before launch. That pedigree wins instant respect with regulators and technically savvy investors.
The process starts with a threat-model workshop, then dives into custom static analysis, symbolic execution, and manual line-by-line review. Expect pointed architectural critiques alongside bug reports; ToB doesn’t just flag issues, it rewrites sections for resilience. For complex exchange stacks—say a proprietary order-matching engine plus EVM custody contracts—clients get specialists in low-level C++, Rust, and Solidity working together.
Depth carries a cost. Six-figure invoices are common, and lead times can stretch past two quarters when bull markets crowd the calendar. Yet founders who invest call it cheap insurance: few projects thoroughly audited by Trail of Bits have later suffered catastrophic exploits. If you are shipping novel code and want the most feared set of eyes in crypto security, book a slot early and clear your schedule.
Hacken: pen testing and proof-of-reserves expertise
Hacken began by breaking into banks and payment apps in Eastern Europe, then applied the same red-team skills to crypto. Today its engineers have audited more than 1,600 Web3 projects and run CER.live, the exchange-security leaderboard that feeds directly into CoinGecko’s Trust Score. In short, the watchdog also publishes the report card.
Where Hacken stands out is full-stack offense. A typical engagement starts with smart-contract review, then expands into cloud-configuration sweeps, API-abuse simulations, and social-engineering drills against support desks. That holistic approach matters for exchanges where a leaked Slack token can be as damaging as a re-entrancy bug.
The firm’s proof-of-reserves audits deserve special mention. After the FTX collapse, many platforms scrambled to prove asset backing; Hacken built automated attestations that cryptographically match hot-wallet balances to liabilities. Exchanges that display the Hacken badge often see faster listing approvals and lower withdrawal limits with institutional desks.
Turnaround times sit near one month, supported by a security staff of more than 100 across Estonia and Ukraine. Pricing is mid-range—higher than a code-only boutique, lower than top U.S. research houses—making it attractive for teams that need both depth and speed. Post-audit, clients can join HackenProof, a managed bug-bounty platform that mobilises 45,000 white-hat hackers on live code. That crowdsourced layer has revealed issues even the internal team missed, a transparency Hacken highlights openly.
Bottom line: if you want a crew that treats your exchange like an adversary would—then hands you a public scorecard at the end—Hacken is the call.
Halborn: full-stack offensive security
Halborn’s backstory feels like a heist film turned professional. Former ethical hackers built a consultancy that attacks every layer of a crypto business, from firewall rules to the Chrome extensions your support team uses. That breadth explains why heavyweight exchanges such as Crypto.com and Binance US invite Halborn in after major upgrades, and why law-enforcement agencies rely on the firm for blockchain-forensics training.
A typical engagement resembles a red-team operation more than a paperwork audit. Engineers launch phishing campaigns, exploit stale Docker images, and chain vulnerabilities until they reach the keys. Only then do they shift to smart-contract review, using in-house fuzzers to stress vault logic. The approach paid off when Halborn uncovered the Rab13s bug class that threatened multiple proof-of-work chains, prompting urgent patches across Dogecoin, Litecoin, and Zcash.
Exchanges juggling both on-chain and traditional fintech stacks value that hybrid mindset. Halborn’s reports arrive with remediation playbooks mapped to SOC 2 and ISO 27001 controls, smoothing the path to regulatory sign-off. After the audit, teams can join a managed purple-team program that reruns exploit simulations each quarter, useful when new product lines ship quickly.
Pricing sits closer to CertiK than Hacken, and lead times hover around six weeks. Given the depth of adversarial testing, most founders view the fee as cheaper than a single public breach. If you want hackers on your side before real ones appear, Halborn is the call.
SlowMist: Asia-focused threat intel
Operate in Asia and you will hear the SlowMist name quickly. Headquartered in Fujian with satellite teams in Singapore and Hong Kong, the firm pairs traditional code audits with live intelligence on phishing rings, malware campaigns, and cross-chain laundering routes. The MistTrack platform has traced nearly 1 billion USD in stolen assets, often alerting exchanges before a scam goes viral.
During an audit, SlowMist reviews the usual Solidity or Rust perimeter, then pivots to region-specific attack vectors such as SMS customer-service scams or supply-chain trojans hidden in Android trading apps. Active channels with Chinese and Korean cyber units let the team update checklists each week.
Wallet forensics is another strength. Analysts replay transaction graphs in real time, flagging abnormal withdrawals that signature-based monitors miss. For exchanges facing strict AML exams, this insight doubles as compliance evidence.
Turnaround is four to six weeks, and pricing is competitive, especially for startups expanding into Mandarin-speaking markets. Public reports skew technical, so non-engineer executives may need a guided walk-through. Still, if your user base spans Beijing to Bangkok and you want auditors who understand both the code and the local tactics, SlowMist is the practical regional ally.
ConsenSys Diligence: Ethereum veteran watchdogs
When your exchange depends on Ethereum smart contracts for custody, staking, or liquidity, few names reassure developers faster than ConsenSys Diligence. The unit grew up alongside MetaMask and Infura, giving its engineers an insider’s view of EVM quirks, from gas griefing to delegate-call pitfalls.
Diligence blends manual review with home-grown tooling such as Mythril for static analysis and Scribble for property-based testing. Reports read like teaching guides: each finding includes exploit scenarios, unit-test snippets, and quantitative risk scores. Clear language helps management gauge severity without reading opcode.
Scope is the trade-off. Diligence focuses on on-chain logic and will not pen-test AWS clusters or mobile apps. Yet its stamp carries weight with investors and major exchanges that vet token listings. Lead times average six weeks, and pricing reflects premium niche skill. For any EVM-heavy component of an exchange, Diligence is the reliable second set of eyes.
OpenZeppelin: security stewards of the EVM
If your exchange token, vesting contract, or governance module imports @openzeppelin/contracts, who better to audit it than the team that wrote the library? OpenZeppelin’s security arm has reviewed blue-chip DeFi systems since 2017, and its engineers know every quirk of upgradeable proxies, access-control patterns, and ERC standards because they designed many of them.
Audits follow a proven rhythm. First, an architecture session surfaces role and upgrade flows. Next, automated scans catch low-hanging issues while senior reviewers inspect interactions between modules, often the real danger zone. Reports land with practical advice such as “rename this function to prevent misuse” or “add a timelock so hotfixes cannot bypass governance.”
Exchanges value the post-audit tooling. OpenZeppelin Defender connects to production contracts, providing alerting, multisig approvals, and pause buttons legal teams appreciate. That operational layer turns a one-time review into continuous risk management without extra DevOps hires.
Expect small-team attention, not assembly-line speed. A mid-size codebase usually finishes in five weeks and costs in the high five figures. Founders often recover that spend when venture desks see “Audited by OpenZeppelin” on the deck; it signals adherence to community standards.
Quantstamp: reliability at scale across multiple chains
Quantstamp began with an ICO vision of decentralised security and now runs a global audit shop that completes more than 200 engagements a year. Engineers use a hybrid model: automated scanners handle boilerplate while senior reviewers focus on economic logic, cross-chain bridges, and novel code paths.
Breadth is the draw. One week the team audits a Solana program handling high-frequency deposits; the next, it reviews Flow contracts for an NFT marketplace or checks Cardano’s consensus upgrade. If your exchange plans products on several chains, Quantstamp’s polyglot expertise saves you from juggling three niche auditors.
Turnaround matches that scale: mid-sized reviews often wrap in three to five weeks, and follow-up verifications arrive in days thanks to stored code models. Pricing sits in the mid tier, making Quantstamp a sensible pick when budgets must stretch across multiple launches.
After the review, clients tap the Quantstamp Security Network for continuous scanning and public “pass” certificates that speed token-listing approvals. No provider is perfect—Wormhole’s later exploit showed upgrades still need fresh eyes—but Quantstamp’s exploit-after-audit rate remains impressively low for the volume of code shipped.
For exchanges that value coverage, consistency, and reasonable cost over boutique flair, Quantstamp delivers the dependable factory line you need.
- ✔ Be Respectful
- ✔ Stay Relevant
- ✔ Stay Positive
- ✔ True Feedback
- ✔ Encourage Discussion
- ❌ Avoid Spamming
- ❌ No Fake News
- ❌ Don't Copy-Paste
- ❌ No Personal Attacks
